If you can see this check that
| next section | prev section | up | prev page | next page |
$ whois napier.ac.uk
Registered For:
Napier University
Servers:
dns0.napier.ac.uk 146.176.1.5
dns1.napier.ac.uk 146.176.2.5
Registrant Address:
Napier University
C&IT
219 Colinton Road~Edinburgh
$ ping www.napier.ac.uk
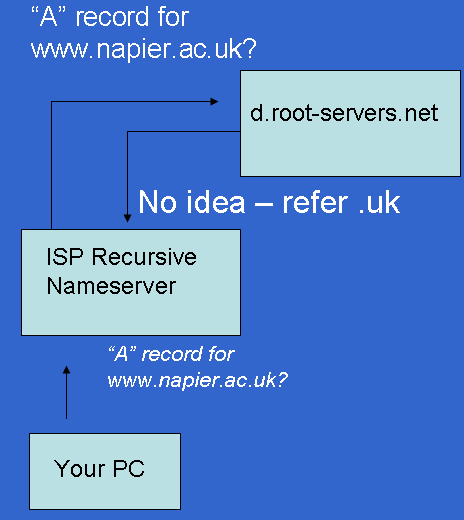
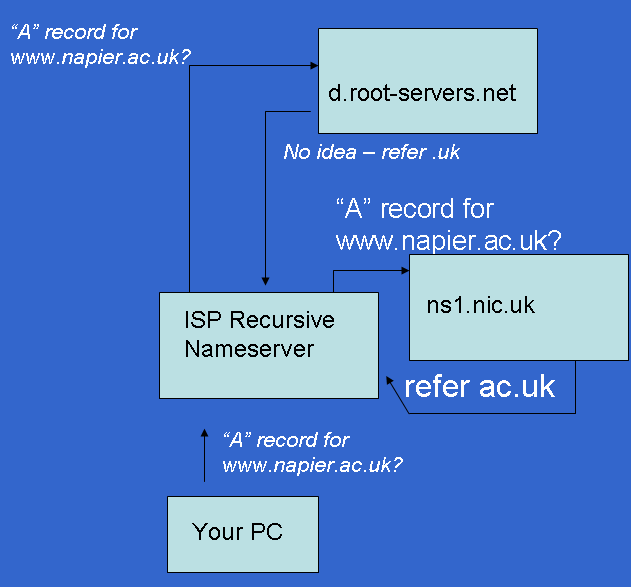
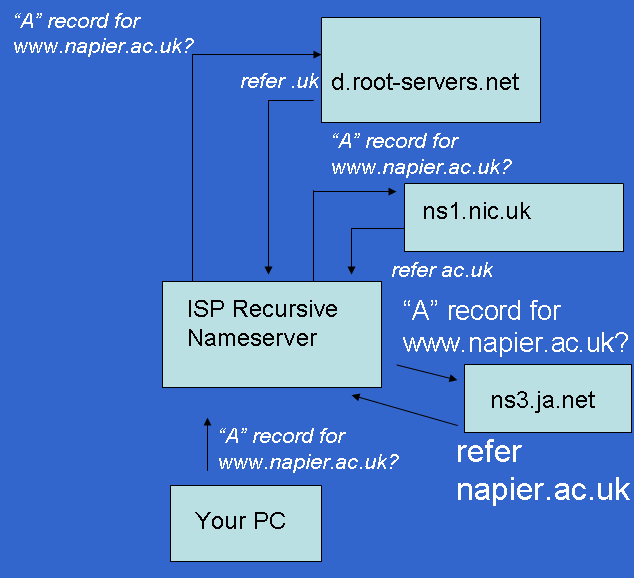
a.root-servers.net. b.root-servers.net. c.root-servers.net. d.root-servers.net.
uk. 172800 IN NS ns1.nic.uk. uk. 172800 IN NS ns2.nic.uk. uk. 172800 IN NS ns3.nic.uk. uk. 172800 IN NS ns4.nic.uk. ;; ADDITIONAL SECTION: ns1.nic.uk. 172800 IN A 195.66.240.130 ns2.nic.uk. 172800 IN A 217.79.164.131 ns3.nic.uk. 172800 IN A 213.219.13.131 ns4.nic.uk. 172800 IN A 194.83.244.131
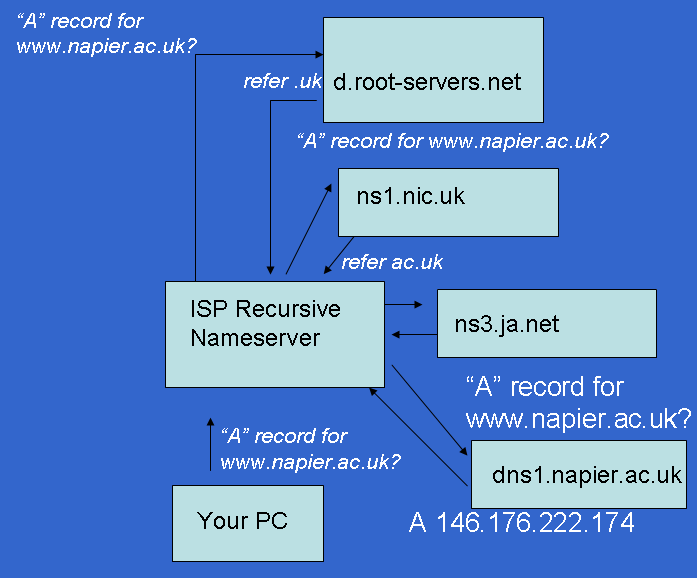
napier.ac.uk. 86400 IN NS dns1.napier.ac.uk. napier.ac.uk. 86400 IN NS dns0.napier.ac.uk. ;; ADDITIONAL SECTION: dns0.napier.ac.uk. 86400 IN A 146.176.1.5 dns1.napier.ac.uk. 86400 IN A 146.176.2.5
$ whois napier.ac.uk Domain servers in listed order: dns0.napier.ac.uk 146.176.1.5 dns1.napier.ac.uk 146.176.2.5
> dig www.napier.ac.uk @dns0.napier.ac.uk www.napier.ac.uk. 86400 IN A 146.176.222.174 ;; AUTHORITY SECTION: napier.ac.uk. 86400 IN NS dns0.napier.ac.uk. napier.ac.uk. 86400 IN NS dns1.napier.ac.uk. ;; ADDITIONAL SECTION: dns0.napier.ac.uk. 86400 IN A 146.176.1.5 dns1.napier.ac.uk. 86400 IN A 146.176.2.5
> dig 222.176.146.IN-ADDR.ARPA ... ;; AUTHORITY SECTION: 222.176.146.IN-ADDR.ARPA. 86400 IN SOA dns0.napier.ac.uk. root.central.napier.ac.uk. 200808271 28800 7200 604800 86400
> dig 174.222.176.146.IN-ADDR.ARPA @dns0.napier.ac.uk -t any ... ;; ANSWER SECTION: 174.222.176.146.IN-ADDR.ARPA. 86400 IN PTR www.napier.ac.uk.
order hosts,bind
search linuxzoo.net net nameserver 10.200.0.1
However, in our experiments we will not be using a chroot for additional security. Instead we will use SELinux. This gives the kernel a set of rules which named must obey, including what files can be opened and what sort of network connections can be made. Fortunately this is all pre-configured in Fedora and thus completely invisible to us as administrators.
In a non-chroot solution this needs only to be stored in /etc/rndc.key If you are (for some reason) using a chroot it must also be copied to /var/named/chroot/etc/rndc.key
zone "." IN {
type hint;
file "named.ca";
};
This tells the daemon to use the root servers listed in named.ca to resolve things not solved by other entries. This can be considered the "default".
options {
directory "/var/named";
forward only;
};
zone "localhost" IN {
type master;
file "localhost.zone";
allow-update { none; };
};
zone "0.0.127.in-addr.arpa" IN {
type master;
file "named.local";
allow-update { none; };
};
$TTL 86400
$ORIGIN localhost.
@ 1D IN SOA @ root (
42 ; serial (d. adams)
3H ; refresh
15M ; retry
1W ; expiry
1D ) ; minimum
1D IN NS @
1D IN A 127.0.0.1
$TTL 86400
@ IN SOA localhost. root.localhost. (
1997022700 ; Serial
28800 ; Refresh
14400 ; Retry
3600000 ; Expire
86400 ) ; Minimum
IN NS localhost.
1 IN PTR localhost.
zone "grussell.org" IN {
type master;
file "grussell.zone";
allow-update { none; };
};
zone "1.1.50.in-addr.arpa" IN {
type master;
file "grussell.rev";
allow-update { none; };
};
$TTL 86400
$ORIGIN grussell.org.
@ 1D IN SOA ns1 admin.grussell.org. (
2004101701 ; serial
3H ; refresh
15M ; retry
1W ; expiry
1D ) ; minimum
1D IN NS ns1
1D IN A 50.1.1.1
www CNAME grussell.org.
ns1 1D IN A 50.1.1.10
$TTL 86400
@ IN SOA ns1.grussell.org. admin.grussell.org. (
1997022700 ; Serial
28800 ; Refresh
14400 ; Retry
3600000 ; Expire
86400 ) ; Minimum
IN NS ns1.grussell.org.
1 IN PTR grussell.org.
10 IN PTR ns1.grussell.org.
host1 IN MX 10 host1 IN MX 20 backuphost IN MX 30 mx.easydns.com.
host1 IN MX 10 smtp1 IN MX 10 smtp2 IN MX 10 smtp3 smtp1 IN A 10.0.0.1 smtp2 IN A 10.0.0.2 smtp3 IN A 10.0.0.3
host1 IN MX 10 smtp smtp IN A 10.0.0.1 IN A 10.0.0.2 IN A 10.0.0.3
www IN A 10.0.0.1 IN A 10.0.0.2 IN A 10.0.0.3 ftp IN A 10.0.0.10 ftp IN A 10.0.0.11
$ tcpdump -n port 53 > dump & $ dig www.napier.ac.uk $ kill -9 %1
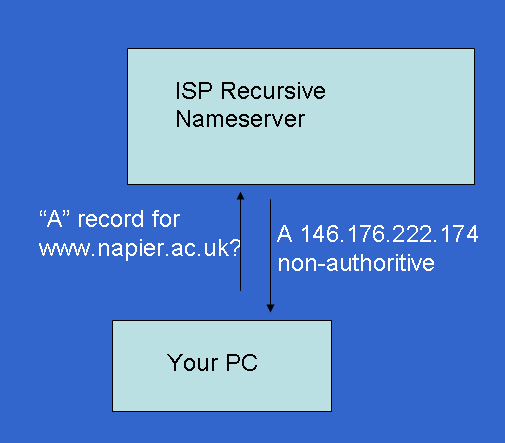
$ cat dump 17:48:54.147146 IP 146.176.162.6.40501 > 146.176.2.5.domain: 6869+ A? www.napier.ac.uk. (34) 17:48:54.148326 IP 146.176.2.5.domain > 146.176.162.6.40501: 6869* 1/2/2 A 146.176.222.174 (120)
$TTL 86400
$ORIGIN broken.net.
@ 1D IN SOA ns1 admin@grussell.org. (
2004101701 ; serial
3H ; refresh
15M ; retry
1W ; expiry
1D ) ; minimum
1D IN NS ns1
1D IN A 10.0.0.1
www CNAME broken.net.
ns1 1D IN A 10.0.0.10.
ns2. 1D IN A 10.0.0.11.
| Centos 7 intro: | Paths | BasicShell | Search |
| Linux tutorials: | intro1 intro2 wildcard permission pipe vi essential admin net SELinux1 SELinux2 fwall DNS diag Apache1 Apache2 log Mail |
| Caine 10.0: | Essentials | Basic | Search | Acquisition | SysIntro | grep | MBR | GPT | FAT | NTFS | FRMeta | FRTools | Browser | Mock Exam | |
| Caine 13.0: | Essentials | Basic | Search | |
| CPD: | Cygwin | Paths | Files and head/tail | Find and regex | Sort | Log Analysis |
| Kali 2020-4: | 1a | 1b | 1c | 2 | 3 | 4a | 4b | 5 | 6 | 7 | 8a | 8b | 9 | 10 | |
| Kali 2024-4: | 1a | 1b | 1c | 2 | 3 | 4a | 4b | 5 | 6 | 7 | 8a | 8b | 9 | 10 | |
| Useful: | Quiz | Privacy Policy | Terms and Conditions |
Linuxzoo created by Gordon Russell.
@ Copyright 2004-2025 Edinburgh Napier University